How Safe are Your Online Passwords?
Last month, some 6,458,020 hashed passwords of LinkedIn users were hacked and uploaded but without usernames. The LinkedIn passwords were stored in an unsalted SHA-1 hash format without the presence of a string (or “salt”) of additional random characters to camouflage the passwords. The intention of “salting” is to make SHA-1 output harder to figure out.
On July 12, 2012, Yahoo! confirmed that some 453,000 unencrypted Yahoo accounts had been compromised and hacked through an older file from the Yahoo! Contributor Network, also known as Yahoo! Voices (added to Yahoo! due to its 2010 purchase of Associated Content). Fewer than 5% of these Yahoo! accounts were said to have had valid passwords. Some members who had registered through Gmail, AOL and other email accounts also had their information exposed on the internet.
A hacker group called the D33ds Company claimed responsibility for posting the log-in information online on the evening of July 11, 2012 (initially on d33ds.co but which was taken down by the morning of July 12, 2012) with the intent to serve a wake-up call rather than a threat. D33ds Company stated that it did not name the Yahoo! service in question. However, the text file is still accessible on the Internet through web sites such as MediaFire (which offers free cloud computing storage). The method of attack is referred to as a SQL injection (which threatens databases accessible through a website). In addition to 453,492 email addresses and passwords visible in plain text, other leaked information included MySQL (the planet’s most popular open source relational database) server variables as well as names of database columns and tables.
The hacked passwords were analyzed by ESET on its EuroSecure blog and the top 10 passwords and the top 10 base words (used to create passwords) were as follows:
Top 10 passwords
123456 = 1666 (0.38%)
password = 780 (0.18%)
welcome = 436 (0.1%)
ninja = 333 (0.08%)
abc123 = 250 (0.06%)
123456789 = 222 (0.05%)
12345678 = 208 (0.05%)
sunshine = 205 (0.05%)
princess = 202 (0.05%)
qwerty = 172 (0.04%)
Top 10 base words
password = 1373 (0.31%)
welcome = 534 (0.12%)
qwerty = 464 (0.1%)
monkey = 430 (0.1%)
jesus = 429 (0.1%)
love = 421 (0.1%)
money = 407 (0.09%)
freedom = 385 (0.09%)
ninja = 380 (0.09%)
writer = 367 (0.08%)
(Source: http://blog.eset.se/statistics-about-yahoo-leak-of-450-000-plain-text-accounts/ )
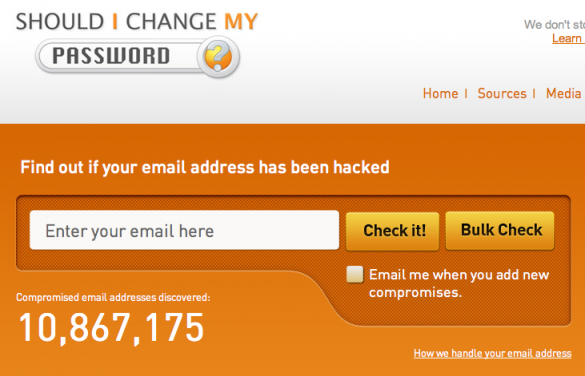
Free email address checking websites such as Should I Change My Password? and Sucuri Malware Labs have been overwhelmed by email users checking whether their email log-in information has been hacked. A July 13, 2012 article on Wired.com offered some good advice for creating a password, including: changing passwords at least every 90 days; keeping the password length to 8 or more characters; substituting symbols for numbers and letters (for example, @ for a); using intentionally misspelled words; avoiding dictionary-based words; avoiding common abbreviations and words spelled out backwards; not using personal information such as birthdays or anniversaries; using at least one number, one symbol, and one lower case/upper case letter; and, using a different password for each account (to reduce vulnerability to hacking). A March 17, 2012 article on PCWorld recommended the creation of a different, secure, easy-to-remember password for every website by using a mixture of numbers, letters, and symbols.
The Microsoft Safety & Security Center offers a password checker to determine the strength of a password. Microsoft does not retain this information. Microsoft also offers suggestions on creating strong passwords, taking into account length, complexity, variation, and variety. However, a strong password CANNOT guarantee 100% protection from hacking although it would make the process more difficult to accomplish.
(See also the blog post by Blog Prince: Do you have a good password? (Part 1) )
Comments